Security TangoWhat is the Security Tango The Security Tango is my name for the dance you have to do every time you want to assure yourself that your computer is free of viruses, spyware, keystroke loggers, backdoors, trojans, and other forms of malware click the Definitions button in the menu to see what all those things mean. Its something you need to do regularly and often daily is not too often The simple act of getting on the Internet and downloading email or going to a Web page can expose your computer to malicious crackers who would love to take over your machine for their own use. Lets Dance To dance the Security Tango, click the Lets Dance link up above. Two left feet Dont worry its not as hard as you might think Which Operating System Do You Use Originally, the Security Tango was mostly for Windows based computers. Im sure that those of you running Linux or a Macintosh used to laugh yourselves sick at all the machinations that your Windows using friends had to go through to keep themselves safe. But dont get too complacent your time is here
The simple act of getting on the Internet and downloading email or going to a Web page can expose your computer to malicious crackers who would love to take over your machine for their own use. Lets Dance To dance the Security Tango, click the Lets Dance link up above. Two left feet Dont worry its not as hard as you might think Which Operating System Do You Use Originally, the Security Tango was mostly for Windows based computers. Im sure that those of you running Linux or a Macintosh used to laugh yourselves sick at all the machinations that your Windows using friends had to go through to keep themselves safe. But dont get too complacent your time is here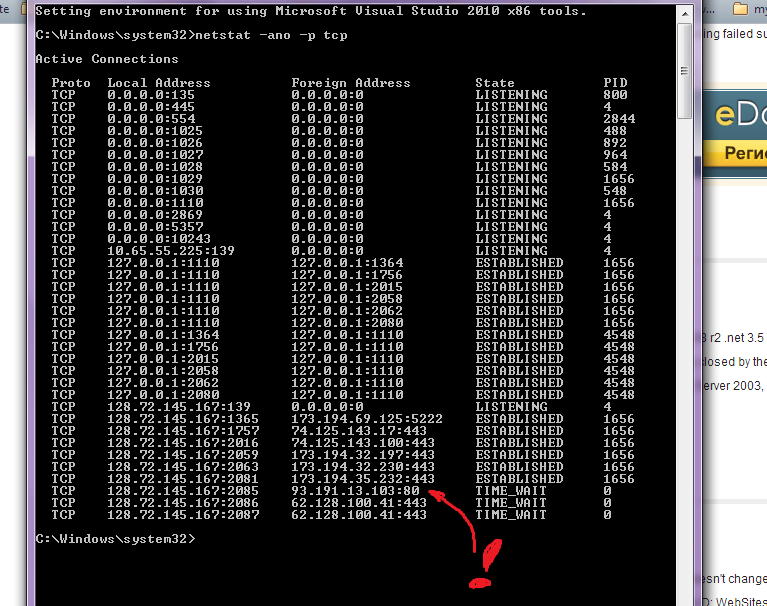 Windows XP Home Pro Run Commands and Short Cuts How To Click Start, Click Run or simply use the shortcut Windows logoR and enter the command Click OK Run. Ephemeral ports are ports that start at a higher range then regular ports. For example when compared to a web server that listens on port 80, ephemeral ports start. What is the Security Tango The Security Tango is my name for the dance you have to do every time you want to assure yourself that your computer is free of viruses. The stateoftheart way of avoiding IP tracking is to use a Virtual Private Network VPN like IP Vanish. The way it works is that you log into the VPN just like you. Kill Active Connection Netstat Windows 2012' title='Kill Active Connection Netstat Windows 2012' />As Linux and the Mac have become more popular, weve see more viruses for them. Yes, there are verified malware programs out there for both the Macintosh and for Linux. You need to protect yourself. Equally importantly, if you dont at least run an antivirus program, you run the risk of passing a virus on to your Windows friends assuming any of them actually talk to you. And thats just not being a good net citizen So Ive split the Tango into parts Windows, Linux, the Macintosh, etc. Ill add more as changes in technology warrant. But you get to all of them by that same Lets Dance button in the menuLatest Virus Alerts. Original release date November 1. Last revised November 2. Systems Affected. Network systems. Overview. This joint Technical Alert TA is the result of analytic efforts between the Department of Homeland Security DHS and the Federal Bureau of Investigation FBI. Working with U. S. DHS and FBI identified Internet Protocol IP addresses and other indicators of compromise IOCs associated with a Trojan malware variant used by the North Korean governmentcommonly known as Volgmer. The U. S. Government refers to malicious cyber activity by the North Korean government as HIDDEN COBRA. For more information on HIDDEN COBRA activity, visit https www. FBI has high confidence that HIDDEN COBRA actors are using the IP addresseslisted in this reports IOC filesto maintain a presence on victims networks and to further network exploitation. DHS and FBI are distributing these IP addresses to enable network defense and reduce exposure to North Korean government malicious cyber activity. This alert includes IOCs related to HIDDEN COBRA, IP addresses linked to systems infected with Volgmer malware, malware descriptions, and associated signatures. This alert also includes suggested response actions to the IOCs provided, recommended mitigation techniques, and information on reporting incidents. If users or administrators detect activity associated with the Volgmer malware, they should immediately flag it, report it to the DHS National Cybersecurity and Communications Integration Center NCCIC or the FBI Cyber Watch Cy. Watch, and give it the highest priority for enhanced mitigation. Denial of service in Qmail by specifying a large number of recipients with the RCPT command. CVE19990144 httpmarc. An AZ Index of the Windows CMD command line ADDUSERS Add or list users tofrom a CSV file ADmodcmd Active Directory Bulk Modify ARP Address Resolution Protocol. System Requirements and Download. Essential NetTools runs on Windows 7 8 8. Windows Server 2008 2012. Both 32 and 64bit versions are supported. Lsof stands for List Open Files. It is easy to remember lsof command if you think of it as ls of, where ls stands for list, and of stands for open file. CurrPorts displays the list of all currently opened TCPIP and UDP ports on your local computer. For a downloadable copy of IOCs, see NCCIC conducted analysis on five files associated with or identified as Volgmer malware and produced a Malware Analysis Report MAR. MAR 1. 01. 35. 53. D examines the tactics, techniques, and procedures observed. For a downloadable copy of the MAR, see Description. Batch Files Examples All Click the floppy disk or icons to download the ZIPped sources. Click the question mark icons to view the MD5 and SHA1 checksums for the. Volgmer is a backdoor Trojan designed to provide covert access to a compromised system. Since at least 2. HIDDEN COBRA actors have been observed using Volgmer malware in the wild to target the government, financial, automotive, and media industries. It is suspected that spear phishing is the primary delivery mechanism for Volgmer infections however, HIDDEN COBRA actors use a suite of custom tools, some of which could also be used to initially compromise a system. Therefore, it is possible that additional HIDDEN COBRA malware may be present on network infrastructure compromised with Volgmer. The U. S. Government has analyzed Volgmers infrastructure and have identified it on systems using both dynamic and static IP addresses. At least 9. 4 static IP addresses were identified, as well as dynamic IP addresses registered across various countries. The greatest concentrations of dynamic IPs addresses are identified below by approximate percentage India 7. IPs 2. 5. 4 percent. Iran 3. 73 IPs 1. Pakistan 3. 43 IPs 1. Saudi Arabia 1. 82 IPs 6 percent. Taiwan 1. 69 IPs 5. Thailand 1. 40 IPs 4. Sri Lanka 1. 21 IPs 4 percent. China 8. 2 IPs, including Hong Kong 1. Vietnam 8. 0 IPs 2. Indonesia 6. 8 IPs 2. Russia 6. 8 IPs 2. Technical Details. As a backdoor Trojan, Volgmer has several capabilities including gathering system information, updating service registry keys, downloading and uploading files, executing commands, terminating processes, and listing directories. In one of the samples received for analysis, the US CERT Code Analysis Team observed botnet controller functionality. Volgmer payloads have been observed in 3. The malware uses a custom binary protocol to beacon back to the command and control C2 server, often via TCP port 8. Secure Socket Layer SSL encryption to obfuscate communications. Adobe Flex Open Source Idea. Malicious actors commonly maintain persistence on a victims system by installing the malware as a service. Volgmer queries the system and randomly selects a service in which to install a copy of itself. The malware then overwrites the Service. DLL entry in the selected services registry entry. In some cases, HIDDEN COBRA actors give the created service a pseudo random name that may be composed of various hardcoded words. Detection and Response. This alerts IOC files provide HIDDEN COBRA indicators related to Volgmer. DHS and FBI recommend that network administrators review the information provided, identify whether any of the provided IP addresses fall within their organizations allocated IP address space, andif foundtake necessary measures to remove the malware. When reviewing network perimeter logs for the IP addresses, organizations may find instances of these IP addresses attempting to connect to their systems. Upon reviewing the traffic from these IP addresses, system owners may find some traffic relates to malicious activity and some traffic relates to legitimate activity. Network Signatures and Host Based Rules. This section contains network signatures and host based rules that can be used to detect malicious activity associated with HIDDEN COBRA actors. Although created using a comprehensive vetting process, the possibility of false positives always remains. These signatures and rules should be used to supplement analysis and should not be used as a sole source of attributing this activity to HIDDEN COBRA actors. Network Signaturesalert tcp any any any any msg MalformedUA content User Agent Mozillar depth 5. YARA Rulesrule volgmermeta description Malformed User Agentstrings s Mozillarcondition uint. A4. D and uint. 16uint. Impact. A successful network intrusion can have severe impacts, particularly if the compromise becomes public and sensitive information is exposed. Useful Command line Commands on WindowsNot really a command per se, but a way to get there. For those of you that find yourself going to Start Run cmd a lot, you can cut down some steps. Say you want to get your IP address. You would normally go Start Run cmd enter. Now instead, go. Start Run cmd k ipconfigThis will run cmd and the command ipconfig, and it will keep the window open. So if I want to quickly get my MAC address physical address, Id do cmd k ipconfig all. All courtesy of Boston.
Windows XP Home Pro Run Commands and Short Cuts How To Click Start, Click Run or simply use the shortcut Windows logoR and enter the command Click OK Run. Ephemeral ports are ports that start at a higher range then regular ports. For example when compared to a web server that listens on port 80, ephemeral ports start. What is the Security Tango The Security Tango is my name for the dance you have to do every time you want to assure yourself that your computer is free of viruses. The stateoftheart way of avoiding IP tracking is to use a Virtual Private Network VPN like IP Vanish. The way it works is that you log into the VPN just like you. Kill Active Connection Netstat Windows 2012' title='Kill Active Connection Netstat Windows 2012' />As Linux and the Mac have become more popular, weve see more viruses for them. Yes, there are verified malware programs out there for both the Macintosh and for Linux. You need to protect yourself. Equally importantly, if you dont at least run an antivirus program, you run the risk of passing a virus on to your Windows friends assuming any of them actually talk to you. And thats just not being a good net citizen So Ive split the Tango into parts Windows, Linux, the Macintosh, etc. Ill add more as changes in technology warrant. But you get to all of them by that same Lets Dance button in the menuLatest Virus Alerts. Original release date November 1. Last revised November 2. Systems Affected. Network systems. Overview. This joint Technical Alert TA is the result of analytic efforts between the Department of Homeland Security DHS and the Federal Bureau of Investigation FBI. Working with U. S. DHS and FBI identified Internet Protocol IP addresses and other indicators of compromise IOCs associated with a Trojan malware variant used by the North Korean governmentcommonly known as Volgmer. The U. S. Government refers to malicious cyber activity by the North Korean government as HIDDEN COBRA. For more information on HIDDEN COBRA activity, visit https www. FBI has high confidence that HIDDEN COBRA actors are using the IP addresseslisted in this reports IOC filesto maintain a presence on victims networks and to further network exploitation. DHS and FBI are distributing these IP addresses to enable network defense and reduce exposure to North Korean government malicious cyber activity. This alert includes IOCs related to HIDDEN COBRA, IP addresses linked to systems infected with Volgmer malware, malware descriptions, and associated signatures. This alert also includes suggested response actions to the IOCs provided, recommended mitigation techniques, and information on reporting incidents. If users or administrators detect activity associated with the Volgmer malware, they should immediately flag it, report it to the DHS National Cybersecurity and Communications Integration Center NCCIC or the FBI Cyber Watch Cy. Watch, and give it the highest priority for enhanced mitigation. Denial of service in Qmail by specifying a large number of recipients with the RCPT command. CVE19990144 httpmarc. An AZ Index of the Windows CMD command line ADDUSERS Add or list users tofrom a CSV file ADmodcmd Active Directory Bulk Modify ARP Address Resolution Protocol. System Requirements and Download. Essential NetTools runs on Windows 7 8 8. Windows Server 2008 2012. Both 32 and 64bit versions are supported. Lsof stands for List Open Files. It is easy to remember lsof command if you think of it as ls of, where ls stands for list, and of stands for open file. CurrPorts displays the list of all currently opened TCPIP and UDP ports on your local computer. For a downloadable copy of IOCs, see NCCIC conducted analysis on five files associated with or identified as Volgmer malware and produced a Malware Analysis Report MAR. MAR 1. 01. 35. 53. D examines the tactics, techniques, and procedures observed. For a downloadable copy of the MAR, see Description. Batch Files Examples All Click the floppy disk or icons to download the ZIPped sources. Click the question mark icons to view the MD5 and SHA1 checksums for the. Volgmer is a backdoor Trojan designed to provide covert access to a compromised system. Since at least 2. HIDDEN COBRA actors have been observed using Volgmer malware in the wild to target the government, financial, automotive, and media industries. It is suspected that spear phishing is the primary delivery mechanism for Volgmer infections however, HIDDEN COBRA actors use a suite of custom tools, some of which could also be used to initially compromise a system. Therefore, it is possible that additional HIDDEN COBRA malware may be present on network infrastructure compromised with Volgmer. The U. S. Government has analyzed Volgmers infrastructure and have identified it on systems using both dynamic and static IP addresses. At least 9. 4 static IP addresses were identified, as well as dynamic IP addresses registered across various countries. The greatest concentrations of dynamic IPs addresses are identified below by approximate percentage India 7. IPs 2. 5. 4 percent. Iran 3. 73 IPs 1. Pakistan 3. 43 IPs 1. Saudi Arabia 1. 82 IPs 6 percent. Taiwan 1. 69 IPs 5. Thailand 1. 40 IPs 4. Sri Lanka 1. 21 IPs 4 percent. China 8. 2 IPs, including Hong Kong 1. Vietnam 8. 0 IPs 2. Indonesia 6. 8 IPs 2. Russia 6. 8 IPs 2. Technical Details. As a backdoor Trojan, Volgmer has several capabilities including gathering system information, updating service registry keys, downloading and uploading files, executing commands, terminating processes, and listing directories. In one of the samples received for analysis, the US CERT Code Analysis Team observed botnet controller functionality. Volgmer payloads have been observed in 3. The malware uses a custom binary protocol to beacon back to the command and control C2 server, often via TCP port 8. Secure Socket Layer SSL encryption to obfuscate communications. Adobe Flex Open Source Idea. Malicious actors commonly maintain persistence on a victims system by installing the malware as a service. Volgmer queries the system and randomly selects a service in which to install a copy of itself. The malware then overwrites the Service. DLL entry in the selected services registry entry. In some cases, HIDDEN COBRA actors give the created service a pseudo random name that may be composed of various hardcoded words. Detection and Response. This alerts IOC files provide HIDDEN COBRA indicators related to Volgmer. DHS and FBI recommend that network administrators review the information provided, identify whether any of the provided IP addresses fall within their organizations allocated IP address space, andif foundtake necessary measures to remove the malware. When reviewing network perimeter logs for the IP addresses, organizations may find instances of these IP addresses attempting to connect to their systems. Upon reviewing the traffic from these IP addresses, system owners may find some traffic relates to malicious activity and some traffic relates to legitimate activity. Network Signatures and Host Based Rules. This section contains network signatures and host based rules that can be used to detect malicious activity associated with HIDDEN COBRA actors. Although created using a comprehensive vetting process, the possibility of false positives always remains. These signatures and rules should be used to supplement analysis and should not be used as a sole source of attributing this activity to HIDDEN COBRA actors. Network Signaturesalert tcp any any any any msg MalformedUA content User Agent Mozillar depth 5. YARA Rulesrule volgmermeta description Malformed User Agentstrings s Mozillarcondition uint. A4. D and uint. 16uint. Impact. A successful network intrusion can have severe impacts, particularly if the compromise becomes public and sensitive information is exposed. Useful Command line Commands on WindowsNot really a command per se, but a way to get there. For those of you that find yourself going to Start Run cmd a lot, you can cut down some steps. Say you want to get your IP address. You would normally go Start Run cmd enter. Now instead, go. Start Run cmd k ipconfigThis will run cmd and the command ipconfig, and it will keep the window open. So if I want to quickly get my MAC address physical address, Id do cmd k ipconfig all. All courtesy of Boston.